What is Code Injection?
Code injection is an attack in which malicious code is injected into an application and then interpreted or executed by it. In PowerBuilder applications, the most common and damaging form is SQL injection - where an attacker manipulates database queries to perform unauthorized operations.
SQL injection in PowerBuilder is particularly serious because it targets the application at its core function: database interaction. A successful attack can expose or destroy years of business data, and in some cases hand an attacker full control over the database server.
Why does SQL Injection target PowerBuilder Applications?
PowerBuilder applications are database-intensive by design. They are built around DataWindows, dynamic SQL, and direct database connections - making them high-value targets, because a successful SQL injection attack against a PowerBuilder application typically reaches mission-critical data directly.
SQL injection attacks against PowerBuilder applications can:
- Access or destroy sensitive data - customer records, financial data, personal information.
- Extract the database schema: table names, column structures, stored procedures.
- Escalate to full database server compromise, denial of service, or hostile takeover.
How does SQL injection work in PowerBuilder code?
The most common SQL injection vector in PowerBuilder is dynamic SQL built through string concatenation where user-supplied values are embedded directly into a query string without validation or escaping.
A typical attack provides a malicious value in a form field where normal input is expected. When that value reaches an unprotected dynamic SQL statement, it alters the query's logic potentially deleting records, bypassing authentication, or extracting data the user was never meant to see.
In PowerBuilder, dynamic SQL statements embedded in PowerScript events and functions are particularly vulnerable and should be reviewed carefully.
Example of non-compliant code - vulnerable to SQL injection:
string query = "DELETE FROM employee WHERE emp_id = '" + Emp_id_var + "'" ; EXECUTE IMMEDIATE: query;
In the example above, if Emp_id_var contains a value like ' OR '1'='1, the WHERE clause becomes universally true and the DELETE affects every row in the table.
Example of compliant code - using parameterized queries:
INT Emp_id_var = 56 PREPARE SQLSA FROM "DELETE FROM employee WHERE emp_id =? " ; EXECUTE SQLSA USING :Emp_id_var;
Parameterized queries pass user input as a typed data value rather than embedding it into the SQL string.
The database engine treats it as data only. It cannot alter the query's structure regardless of what the input contains.
Visual Expert can automatically perform this verification to identify such security vulnerabilities.
How to find SQL injection vulnerabilities with Visual Expert
Visual Expert automatically scans your entire PowerBuilder codebase for dynamic SQL patterns vulnerable to code injection.
Here is how to locate all affected objects in one pass.
List all code injection vulnerabilities across the application
- In the Main View, click on [Code Inspection for PowerBuilder].
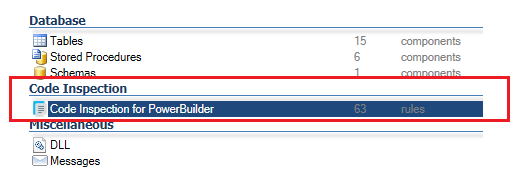
- In the Navigation Bar, click on [Security Vulnerabilities].
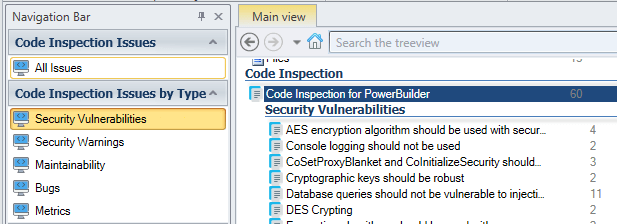
- Select the rule “Database queries should not be vulnerable to injection attacks”.
- Select [Issues Found] in the Navigation Bar.
Visual Expert lists all the events and functions with SQL queries vulnerable to Code Injection.
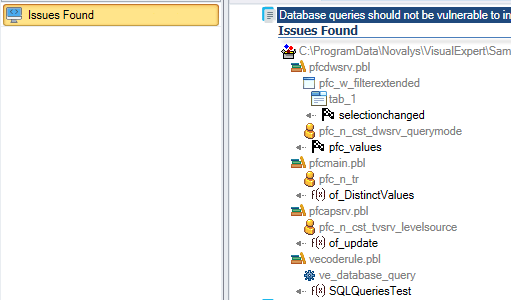
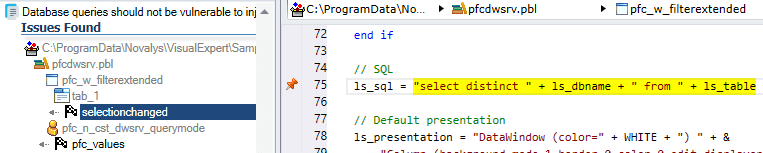
- Select a method from that list.
The instructions generating this vulnerability are highlighted in the code.
- To fix a 'Code Injection' issue, select the PowerBuilder function in the treeview.
- In the Navigation Bar, click on [Open in PB IDE].
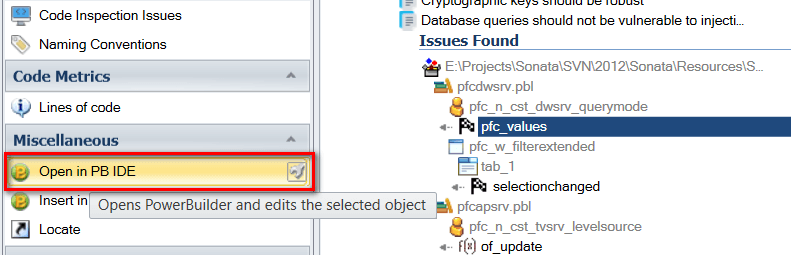
Visual Expert will open the corresponding target, object and Powerscript in the PowerBuilder IDE, under the condition that PB was previously opened with the proper Workspace.
You can then perform modifications and build/save your PB project.
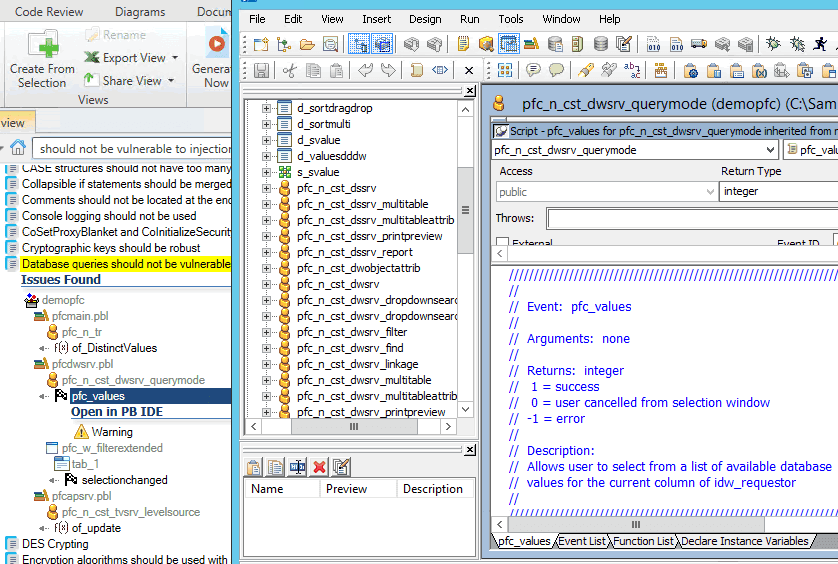
After the next code analysis, Visual Expert will update 'Code Inspection' results according to your modifications.
Inspect a particular Object, Library, Package or Method
In case you wish to focus on a particular piece of code, you can follow these steps:
- In the Visual Expert Treeview, select the piece of code you wish to inspect.
For example a procedure.
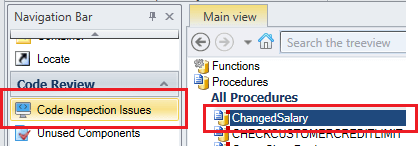
- In the navigation bar, click on “Code Inspection Issues”.
- Follow the steps 4 to 7 explained above.
Beyond SQL injection: other injection risks in PowerBuilder
SQL injection is the most prevalent form of code injection in PowerBuilder, but Visual Expert also detects two additional injection vulnerability types that affect applications processing user input:
- Path traversal attacks - when PowerBuilder code dynamically constructs file system paths from user input, attackers can inject sequences like ../ to access directories outside the intended scope.
- OS command injection - when PowerBuilder code executes operating system commands based on user-supplied values without validating the command name, attackers can inject arbitrary system commands.
Both are covered by Visual Expert's PowerBuilder security vulnerability scanning rules.
